We Launch Data Guard Version 3.12 - An Update for Safer Transfers
link22 now launches an updated version of our core product within Secure Transfer, Data Guard. With improved functionality and increased flexibility in version 3.12, we now offer even stronger protection for critical data.

Data Guard - Protection Against Cyber Threats
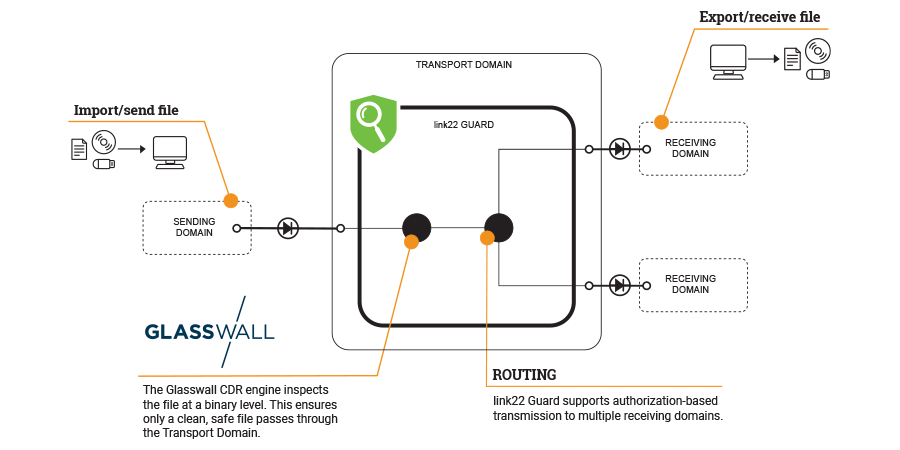
Data Guard is a central component in link22's offerings within Secure Transfer. The product inspects files and approves or denies them before they enter or leave a system. Data Guard enables secure, controlled, and traceable import of program updates to secure domains. Filters and antivirus programs check files for potentially harmful content.
Enhanced Functionality and Increased Flexibility
Data Guard can also be used to verify and approve which documents are allowed to be exported from sensitive networks. The product is highly flexible and configurable - it comes with a range of filters designed to detect unwanted files, and also allows you to easily add your own filters.
Data Guard 3.12 - A New Era of Cybersecurity
link22 is now launching version 3.12 of the Data Guard product. "We currently have quite a few customers using our Data Guard, both in the private and public sectors," says Marcus Ekbäck, Business Area Manager for Cross Domain Solutions at link22. "The content of our new version is based on requests from our customers, but also improvements that we see make a good product even better."
Protect Your Organisation with Data Guard 3.12
With Data Guard 3.12, you can feel more secure in the knowledge that your company's critical data is protected against cyber threats. Whether you need to ensure the import of program updates or control which documents are allowed to be exported from your network, Data Guard 3.12 is a reliable solution.
To learn more about how Data Guard 3.12 can enhance your organization's cybersecurity, visit our product page for Data Guard.

Contact us!
Marcus Ekbäck
sales@link22.se
+46 13-13 24 00