Neutralizes Files
Content Disarm and Reconstruction neutralizes the content of files. If CDR is set up in the secure solution for importing/exporting information, the file is taken apart, verified, and reconstructed into a secure file with the same informational content. This makes it much harder for perpetrators to send unwanted code hidden in regular files.
Protection against the unkown
Firewalls and filters search for known threats, viruses, or other software classified as malicious. Therefore, they do not protect against undiscovered threats, such as Zero Day attacks. CDR solves this problem by transforming every file into a harmless one, regardless of whether the original file was malicious or not.
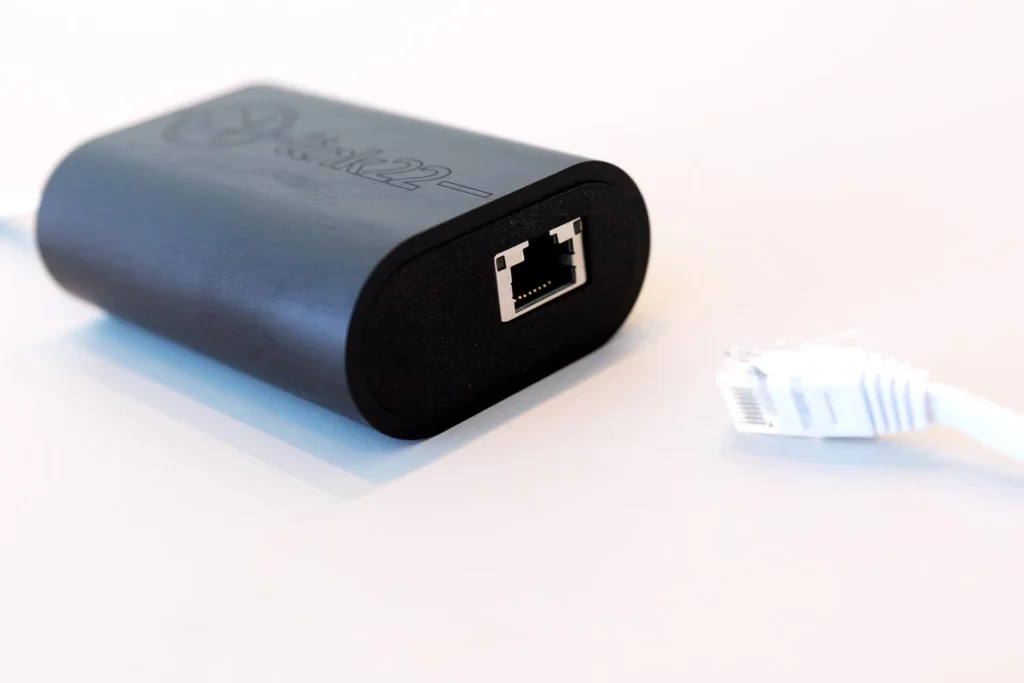
Perfect for link22 Cross Domain Solution
link22 has developed a seamless integration to make it easy to combine our products with Glasswall’s CDR. The CDR feature is an excellent complement to link22’s Cross Domain Solution. This technology can be used for both import and export of information, and it can also be applied between security domains.
We are satisfied with Outpost, it is easy to use and gets the job done. We recommend it to our customers.
Anonymous customer
We are very happy with the support from link22, they always answer fast in a professional manner.
Anonymous customer
We are generally happy with Outpost and the support received from link22.
Anonymous customer
CDR in four steps
1 – Inspect
Three layers of the file are inspected to validate that its digital DNA aligns with the manufacturer’s specifications for a harmless file. Actions are taken immediately where discrepancies are detected.
2 – Cleanse
Active content of a risky nature (e.g. macros and embedded links) is cleansed and removed, based on your policy – only those users who need active content will receive it.
3 – Re-create
The file is reconstructed according to the manufacturer’s standard for a harmless file type, ensuring that the file is clean and free from threats.
4 – Deliver
The user has imported a secure, approved, standardized, and trusted file.
Details about CDR
Functions
- Secure transmission of documents, image and media files
- Managed source code and CI/CD pipeline transfer
- Image conversion to alternative formats such as bitmap
- Prevention of data loss through methods such as word search and editing/proofreading
- Proactively prevent unknown threats from infiltrating your IT system